The Future of Secure Communications, a study from Forrester Consulting that Element commissioned, shows that 79% of technology leaders at large organisations feel their sanctioned video conferencing tools fall short in adequately supporting secure and reliable partner communications. Likewise, 76% said their sanctioned voice tools were not well suited to secure communication.
Sanctioned communications tools falling short for security and reliability
- Sanctioned video conferencing tools
- Sanctioned voice tools
- Sanctioned enterprise/work email
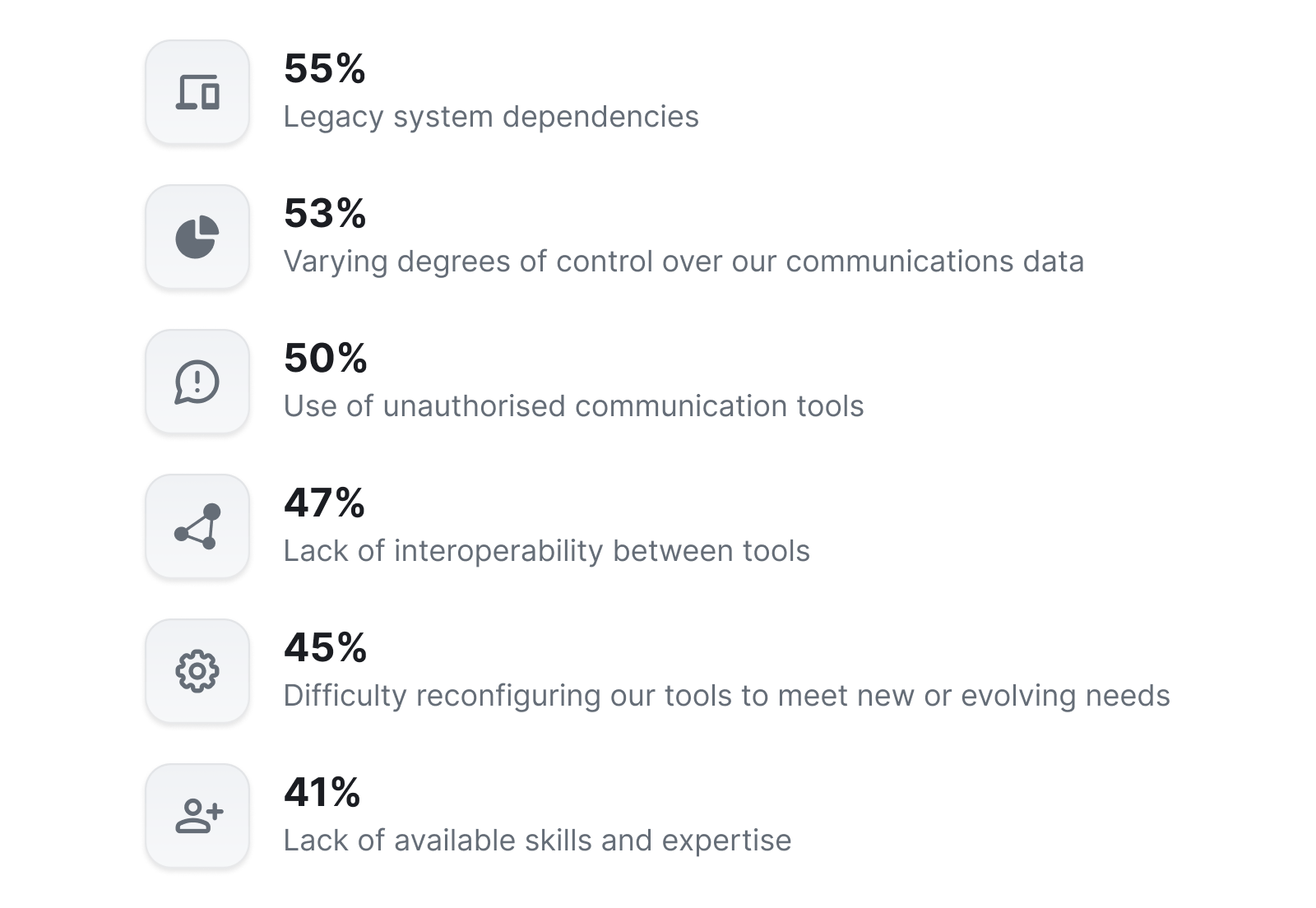
A number of other obstacles stand in the way of leaders’ ability to improve the security and reliability of real-time communications. Among the most common are legacy systems, a lack of control over communications data and a lack of interoperability particularly when communicating with external parties.
Significant obstacles to improving the security and reliability of real-time communications
Addressing the lack of interoperability is a driving ambition behind Matrix, a decentralised open standard for real time communications. All Matrix-based systems benefit from the native interoperability offered by the protocol itself, which also supports digital sovereignty and end-to-end encryption.
Element Call for maximum security VoIP
Element Call is an open source end-to-end encrypted video and voice conferencing solution built on the Matrix protocol for secure communication.
We’re developing Element Call to provide the best possible security properties with compulsory end-to-end encryption, supporting sender verification, forward secrecy, post-compromise secrecy, zero-trust decentralisation and cross-domain capability. It achieves this by building on the foundations of Matrix as a mature, audited [1], open standard protocol for secure communication, which provides:
- Compulsory end-to-end encrypted communication between devices via the Double Ratchet (“Signal Protocol”). This means that user data is protected even if the server is compromised, as only the participating devices have the keys required to decrypt the data. This also provides forward secrecy (meaning that even if the current key data is leaked, historical data will not be compromised), and post compromise security (meaning that future data will also be protected, even if the current keys are leaked).
- Cryptographic identity verification, protecting against interception or impersonation, by allowing users to verify the identity of their correspondents over an existing trusted communication channel - such as comparing a short authentication string (sequence of emoji or numbers) or by scanning a QR code in person. Identity verification is critical, as there is no point in end-to-end encryption if you end up talking to an attacker.
- Cryptographic agility - Matrix is built to evolve, and all parts of the protocol can be upgraded under the terms of the open governance model of the Matrix specification [2]. All current implementations from Element share the same Rust encryption implementation (vodozemac), allowing encryption changes to be implemented and audited in one place. Ongoing futureproofing work includes Post Quantum resilience via Kyber post-quantum KEM and PQXDH key exchange [3], as well as support for Messaging Layer Security (MLS, RFC9420) for improved scalability for group encryption [4].
- Enterprise identity management - integrating with authentication systems such as OpenID Connect to ensure that access to the platform is restricted to authorised users, including restricting access to calls based on group access permissions.
- Decentralised communication - letting multiple independent deployments interoperate together in a multilateral zero-trust architecture, leveraging Matrix’s decentralised Access Control capabilities [5], while still providing the same secure communication guarantees as if in a single instance. Moreover, these deployments can operate at different information classification levels (e.g. NATO SECRET to UK OFFICIAL SENSITIVE) and still interoperate for multiparty VoIP and messaging and file transfer thanks to Matrix’s support for cross-domain and cross-classification communication via hardware-based Cross Domain Gateway solutions.
Element Call is effectively an application built on top of the Matrix protocol (much as Firefox is an application built on top of the Web) and so directly inherits Matrix’s security properties. It can be used as a standalone application, but when integrated with a full communication client such as Element Web/Desktop or Element X (Mobile), it leverages the full set of identity verification, user verification, decentralised access control provided by Matrix.
Call media is end-to-end-encrypted using WebRTC Insertable Streams, using S-frames to encrypt on a frame by frame basis, and in turn each participant has its own unique series of keys for each stream of media it sends. These keys are replaced every time the call participants change, providing forward secrecy, and the keys are exchanged over the same Double Ratchet encryption used by Matrix for all other encryption - ensuring that if the users have verified their identity by securely scanning QR codes or exchanging short authentication strings, there is no way for an attacker in the network or on the server to intercept their communication.
Element Call is scalable to thousands of users per call by utilising LiveKit [6] as the underlying media server responsible for relaying streams between devices. Element Call can also operate “full mesh” for smaller conferences without a dedicated media server for ad hoc decentralised conferencing - and is built to support heterogeneous cascaded decentralised conferences: with conferences cascading over entirely separate instances as required.
The best end-to-end encryption does not help if the hurdles to use the technology are too large for practical use or if the system includes leaks by design. Element Call addresses both challenges. To avoid insecure meeting invites being sent via email to participants, meeting invitation can happen over a secured, end-to-end encrypted and verified Matrix chat channel. It is impossible for an attacker to even get hold of the meeting invite.
Element Call also deliberately does not integrate unencrypted gateways, such as using SIP to interoperate with a normal phone line, as this would provide a direct attack vector. Instead, a user-friendly mobile client on iOS and Android can be used to receive the meeting invite or the direct video call and also to participate in the video conference. Via pinned certificates, the client mitigates the risk of TLS man-in-the-middle attacks in case a Certificate Authority is compromised (although even in the event of a TLS man-in-the-middle attack, Matrix’s end-to-end encryption protects the call media from interception).
This is where we’re headed when it comes to security with open source conferencing tools. For more info, please feel free to get in touch.
You can download The Future of Secure Communications study here.
- Audited by BSI (German Federal Office for Information Security) as Projekt 604 – Codeanalyse für Opensource Software (CAOS2) Analyseergebnisse Arbeitspaket 2: „Kommunikationssystem Matrix“, and by Least Authority (funded by Gematik, the German healthcare interop agency): https://matrix.org/blog/2022/05/16/independent-public-audit-of-vodozemac-a-native-rust-reference-implementation-of-matrix-end-to-end-encryption/
- https://spec.matrix.org
- https://github.com/matrix-org/vodozemac/pull/120
- https://arewemlsyet.com
- https://matrix.org/blog/2020/06/16/matrix-decomposition-an-independent-academic-analysis-of-matrix-state-resolution/
- https://livekit.io/



